Track record
- 9+ years of production AWS architecture
- 50+ projects across fintech, healthcare, e-commerce, SaaS, and enterprise
- $6M+ (50 Crore+) in documented client savings
- Currently at ASTM International
About InfraTales
InfraTales exists because too much infrastructure content stops at the demo. This publication is for engineers and technical leaders who need the trade-offs, the failure modes, the cost picture, and the operational reality.
Credentials
Consulting portfolio
KFC Thailand -- Serverless migration, 5M+ orders/month at sub-200ms latency.
ASTM International -- Enterprise cloud architecture, SOC2 compliance, 70% reduction in manual setup.
ProdigyBuild -- Serverless SaaS platform, 99.9% availability, 40% cost reduction.
AppGambit -- Cloud-native event processing, 1M+ requests/minute, 99.99% uptime.
ProtectOnce -- API security infrastructure on AWS.
How articles are made
Every InfraTales article starts with a real IaC project - actual CDK or Terraform code that was written to solve a real problem. Not a hypothetical. Not a demo. An actual codebase with real IAM policies, real VPC configurations, and real deployment scripts.
The code gets sanitized (credentials stripped, account IDs redacted, internal domain names replaced), then analyzed for the architecture decisions it contains. A content brief captures the trade-offs, failure modes, cost implications, and operational concerns. The article is drafted, run through quality checks (secret scanning, structure validation, SEO optimization), then humanized to sound like a person wrote it - because a person did write the editorial layer on top.
The sanitized code gets published as a public GitHub repo under the InfraTales organization. Every article links to its repo, and every repo links back to its article. Code and explanation stay connected.
What you won't find here
No sponsored content. No affiliate links. No "top 10" listicles. No content written to hit a publishing calendar when there's nothing worth saying.
No vendor-neutral fence-sitting. If CDK is the right tool for a specific situation, the article says so. If Terraform wins under different constraints, it says that too. Opinions are stated, reasoning is shown, and the reader decides.
No "it depends" without a recommendation. Every article, pattern, and comparison gives you a clear default answer and the specific conditions that would change it.
Editorial philosophy
AWS architecture, platform engineering, observability, cloud cost optimization, AI infrastructure, and explaining why a design is right or wrong under real constraints.
Opinionated, production-first, and explicit about trade-offs. No beginner padding, no vague "best practices" without context, and no pretending cost or operations are afterthoughts.
Start with the flagship articles, move into a topic hub, and use the resource library when you need to turn ideas into reviewable decisions.
Flagship work
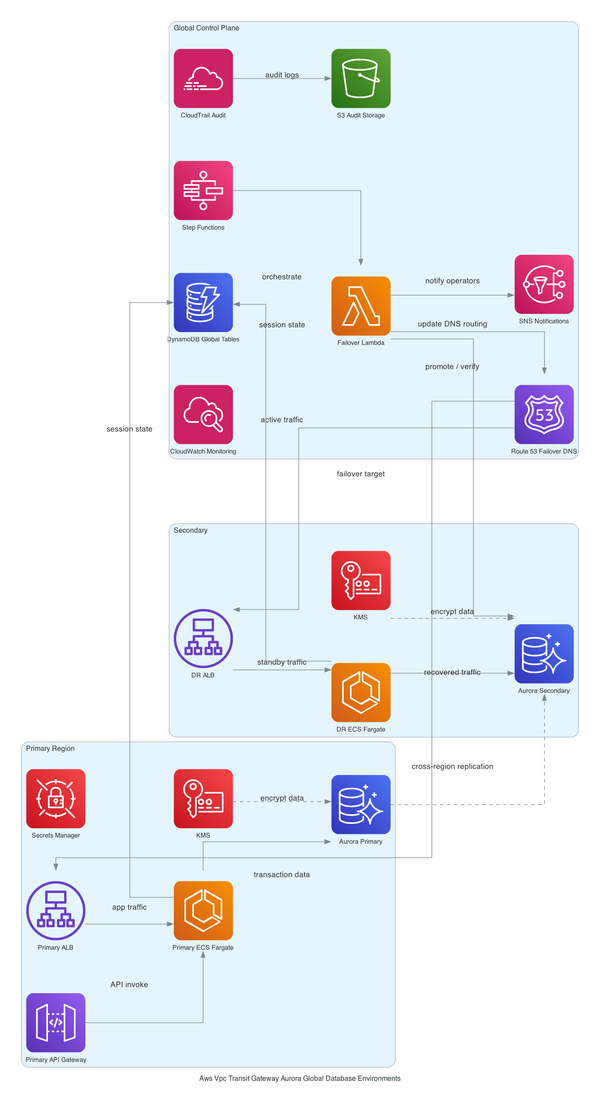
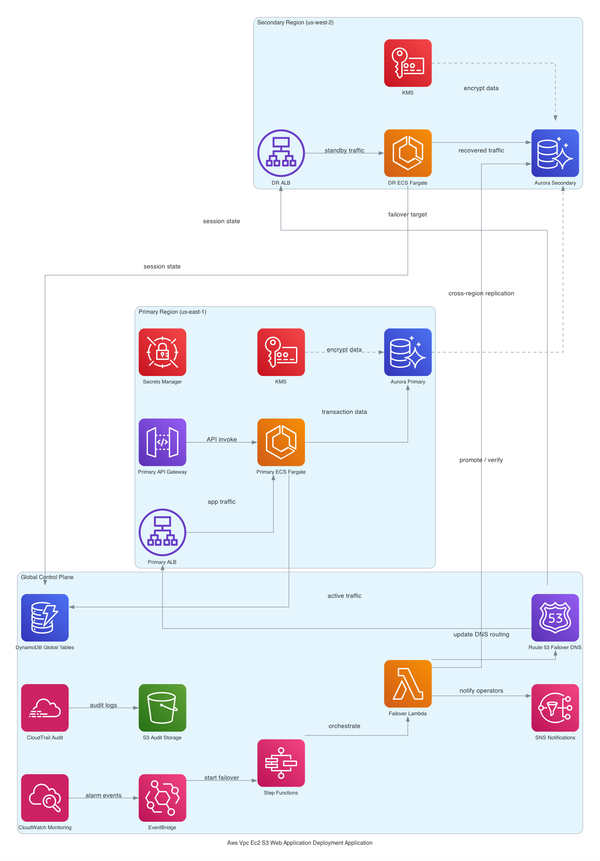
Running dev, staging, and prod on separate VPCs sounds clean until you need them to talk — and your Aurora failover has never actually been tested. This post walks through a real CDK TypeScript stack wiring Transit Gateway, Aurora Global Database, ECS Fargate, and Global Accelerator across three env
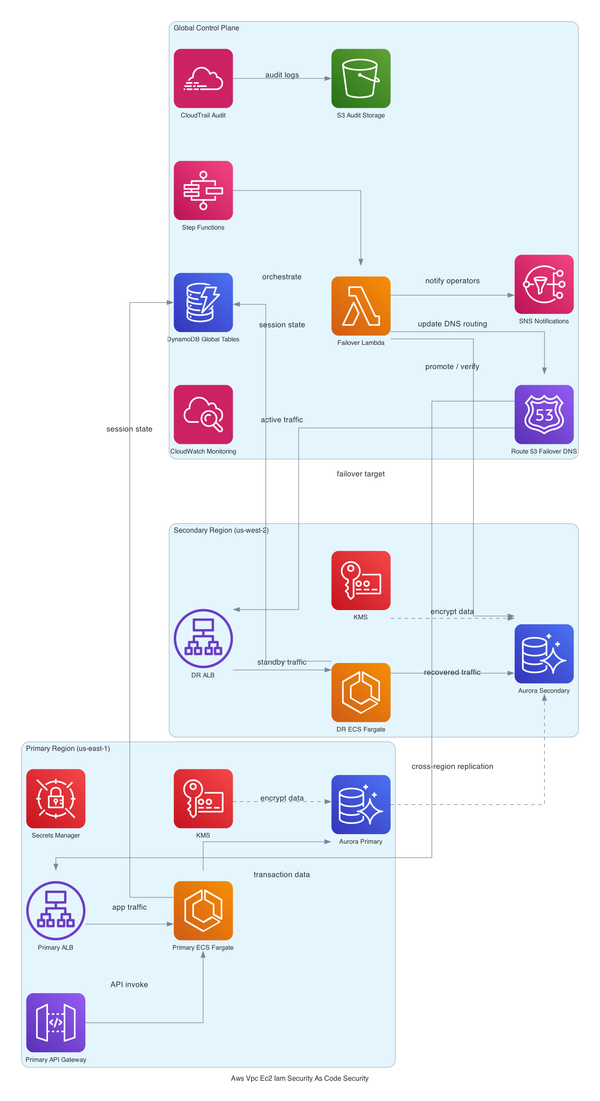
Most AWS accounts get hardened once by someone who no longer works there. This post walks through a CDK TypeScript stack that encodes VPC isolation, KMS key policies, IAM least-privilege, AWS Config rules, WAF, and CloudTrail into version-controlled, PR-reviewable infrastructure — so your security p
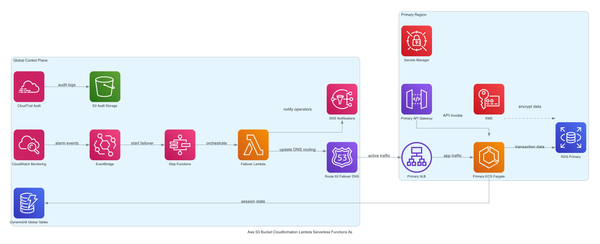
Most S3-to-Lambda setups skip CloudTrail data events entirely and pay for it later with brittle fan-out and zero audit trail. This post walks through a CDK TypeScript stack that routes S3 events through EventBridge properly — VPC placement, KMS encryption, Secrets Manager, cost model, and the failur
Wiring CodePipeline, CodeDeploy, and Auto Scaling in CDK sounds straightforward until your first real scale event cracks the deployment. This post walks the full architecture - VPC, ALB, ASG, SSM config, and the lifecycle hook settings that keep deploys clean under load.
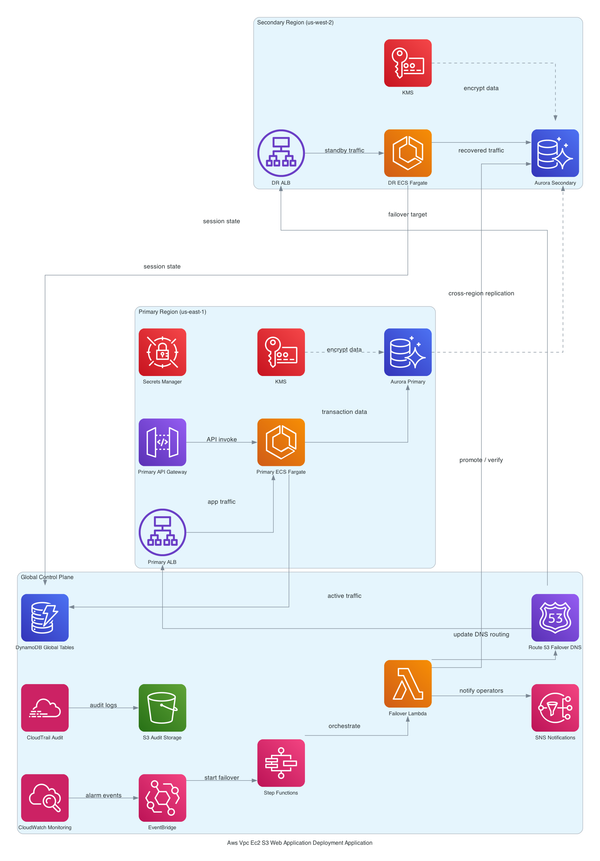
Most CDK tutorials stop at 'it deployed.' This one covers the full aws cdk web application deployment stack - VPC isolation, Fargate on private subnets, Aurora with KMS, CloudFront, Secrets Manager rotation - and the six operational gaps that will wake you up at 2am if you skip them.
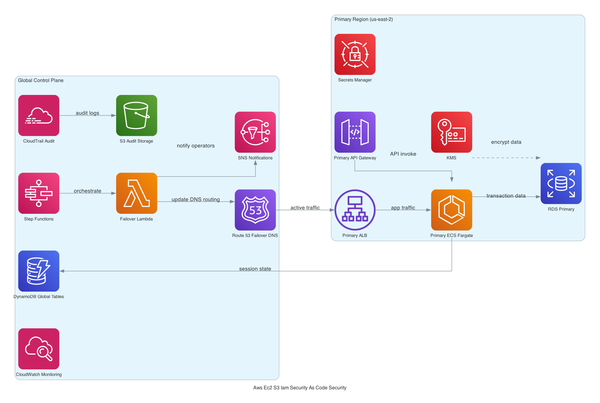
Your IAM permissions are a wiki page nobody trusts. This post walks through a CDK TypeScript stack that encodes KMS encryption, IAM roles, and RDS storage security as versioned, reviewable code - and covers the operational traps most tutorials skip entirely.